Valiant Communications is an ISO 9001:2015, ISO 10001:2018, ISO 14001:2015, ISO 27001:2013 and ISO 45001:2018 certified equipment manufacturer.
Links
Products
Teleprotection over E1, C37.94,
MPLS-TP, MPLS / IP, IEC-61850 GOOSE
VCL-PMU-30, Phasor Measurement Unit (PMU)
VCL-PDC, Phasor Data Concentrator (PDC)
Products
GPS / GNSS, Primary Reference Clocks (G.811)
PTP IEEE-1588v2 Grandmaster, PTP Slave, PTP Transparent Clock
GPS to IRIG-B, GPS to 1PPS Servers
Time Distribution, IRIG-B, 1PPS, RS-232 / RS-485
SDH with MPLS-TP & SONET Multiplexers
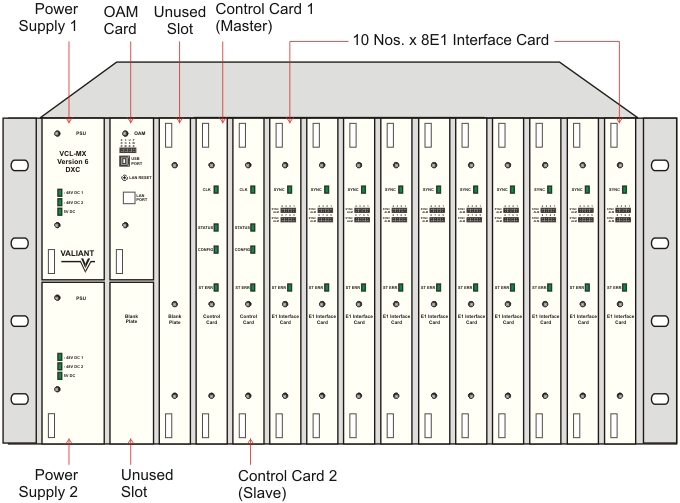
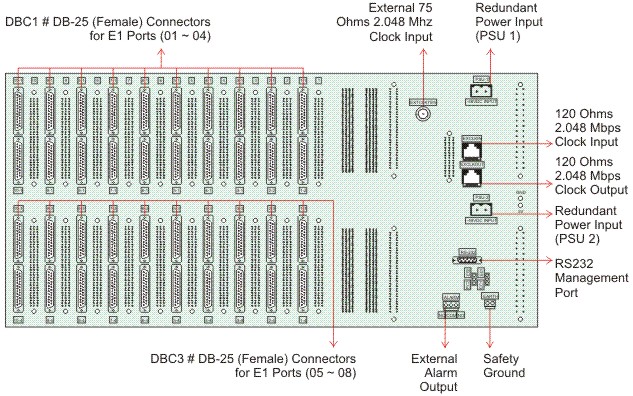
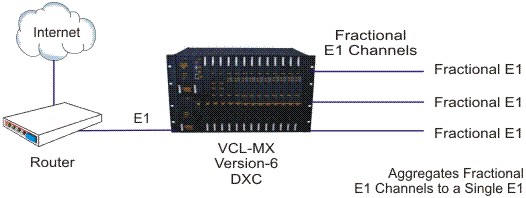
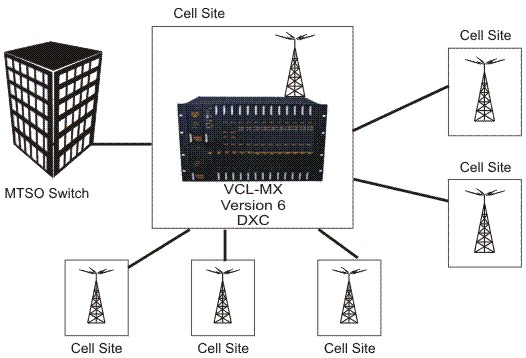
E1 PDH & Digital Cross Connect
Products
IP over TDM / Ethernet over TDM
TDM over IP / Ethernet / Packet / MPLS
E1 / T1, 1+1 Automatic Protection / Failover
1+1 Ethernet Failover / AB Fallback Switch
Groomer (Hi-Z Non-Intrusive Monitoring) - E1, T1 and STM-1
E1 and T1 Echo Cancellers & VQE
Serial to Ethernet and MODBUS Converters
Patch Panels, AC DC Converters, Passive Products